Get more control and visibility over who's accessing your network
Zero Trust Network Isolation protects your network against data breaches, insider threats and malware without complex on-premise setups.
Increased protection of highly sensitive information
Simplified setup, scalability and management
Affordable for businesses of any size

Our collaboration with Jimber as their distributor has been smooth since day one. Communication regarding resellers, end customers, and administration runs seamlessly. The technical staff has insight in both simple and complex end user situations. They are always ready to assist both partners and end customers with their innovative solution.
 Jimber - Cybersecurity Experts€€€
Jimber - Cybersecurity Experts€€€Traditional security solutions are outdated!
Many security solutions that are in use today are perimeter-based. These solutions were developed long before the cloud and remote work became a thing. Therefore, it’s getting harder each day to protect sensitive data from ever-evolving cyberthreats.
The main risks are the inability to protect against internal threats because of limited visibility into what’s happening inside the network perimeter, very limited protection for remote workers, and complexity which leads to misconfigurations and security vulnerabilities.
These networks are easy to breach and once a hacker gets access, they can move around freely across the entire network without getting noticed.
How legacy security solutions fall short
If a hacker is able to bypass traditional VPNs or Network Segmentation, they will have broad network access and thus full control over your company’s industrial OT system.
Every location needs one
Extremely time-consuming to set up
They cost thousands per location
Annoying downtimes during installation
Limits visibility into network traffic
Increased network complexity
Difficult to manage and maintain
Often requires additional expensive hardware & security tools on top
Protect your data with Zero Trust Network Isolation
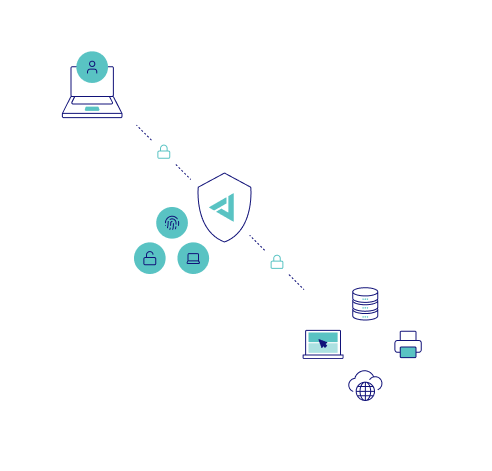
Network Isolation is based on Zero Trust architecture which uses a “never trust, always verify” approach to grant access to corporate applications, data, and services. Zero trust security assumes that every device and user accessing the network is potentially compromised and must be authenticated and authorized. This approach is based on the principle of least privilege: users and devices are granted access only to the resources they need to perform their job.
Once access is granted, the user or device is isolated from the rest of the network using micro-segmentation. Creating these isolated segments ensures that even if a user or device is compromised, the damage cannot spread to the rest of the network.
Why Jimber is the best solution for Zero Trust Security
Easy to set up and maintain
Jimber’s cloud-native approach makes this Zero Trust security solution easy to scale, hardware independent, and highly compatible with your current solutions.
User-based security
Secure network access is based on the user’s identity and permissions, not on their location or the device they’re using.
Limited downtime
Thanks to phased deployment that doesn’t require any hardware installations, the implementation of Zero Trust Network Isolation will go by almost unnoticed.
Control from a central location
You don’t need on-premise hardware for secure network access. Instead, you can manage and monitor all network activity from one location through the Network Isolation Portal and Network Isolation Access Controller.
Granular access control
The portal makes it easy to track which users and devices are accessing specific gateways and resources. Moreover, it allows administrators to create and edit roles and permissions without much effort.
More affordable than legacy solutions
Network Isolation’s cloud-native setup doesn’t require long-dreaded installations or expensive tools. It’s a safer and more affordable security solution than traditional Firewall or VPN systems.
24/7 Support
Jimber offers 24/7 support for its all-in-one solution, meaning all your security questions can be handled through one point of contact.
Why Jimber is the best solution for Zero Trust Security
Easy to set up and maintain
Jimber’s cloud-native approach makes this Zero Trust security solution easy to scale, hardware independent, and highly compatible with your current solutions.
User-based security
Secure network access is based on the user’s identity and permissions, not on their location or the device they’re using.
Limited downtime
Thanks to phased deployment that doesn’t require any hardware installations, the implementation of Zero Trust Network Isolation will go by almost unnoticed.
Control from a central location
You don’t need on-premise hardware for secure network access. Instead, you can manage and monitor all network activity from one location through the Network Isolation Portal and Network Isolation Access Controller.
Granular access control
The portal makes it easy to track which users and devices are accessing specific gateways and resources. Moreover, it allows administrators to create and edit roles and permissions without much effort.
More affordable than legacy solutions
Network Isolation’s cloud-native setup doesn’t require long-dreaded installations or expensive tools. It’s a safer and more affordable security solution than traditional Firewall or VPN systems.
24/7 Support
Jimber offers 24/7 support for its all-in-one solution, meaning all your security questions can be handled through one point of contact.
Find out how we can protect your business
In our demo call we’ll show you how our technology works and how it can help you secure your data from cyber threats.

Need an affordable cybersecurity solution for your customers?
We’d love to help you get your customers on board.
White glove onboarding
Team trainings
Dedicated customer service rep
Invoices for each client
Security and Privacy guaranteed